Cyber Range Sandbox
Overview
Rapidly reconfigure complex, real-world cyber threat sandboxes in seconds.
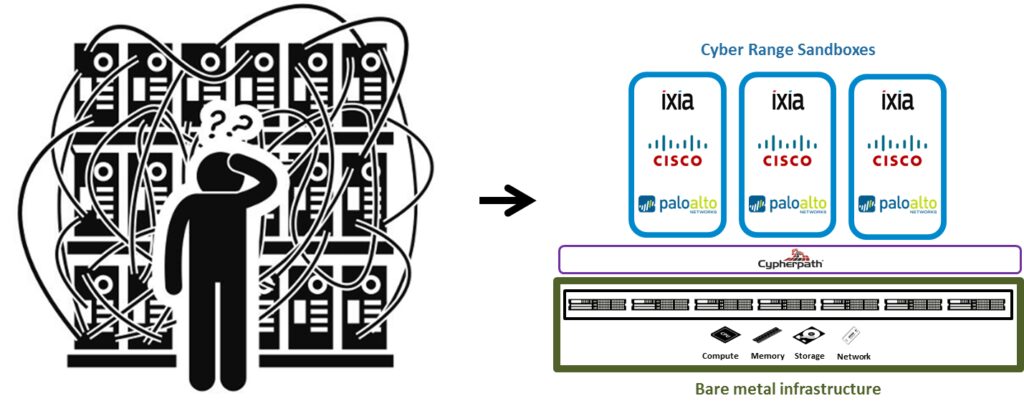
As cyber threats continue to grow and diversify, enterprises recognise the need for cyber range security solutions that effectively simulate real-world cyber threat scenarios. However, most organisations lack the budget and manpower resources required to deploy large scale, infrastructure heavy, complex, sandbox environments. Businesses need an efficient and low cost solution for build, run, rinse, and repeat use cases. They need to rapidly provision truly full stack environments and make them simultaneously available as-a-service in seconds to multiple tenancies, groups, and users.
Our Cyber Range Sandbox solution gives enterprises the ability to rapidly reconfigure complex, real-world cyber threat sandboxes in seconds that require no specialised skills to deliver. The solution is an easy to deploy software suite, all contained within a single file, that loads on to any x86 stack. This allows you to rapidly model entire environments and publish them as a single file to easily distribute, provision, and run anywhere. Virtual machines from any source can be included inside our solution including those from vendors such as Juniper or Cisco, along with complete environments such as Openstack.
Cyber Range Sandbox Overview
Our solution is fully virtualised and depends on Cypherpath’s Software Defined Infrastructure. Cypherpath can be installed onto any bare metal x86 server and then leverages true hyperconvergence to integrate compute, networking, virtualisation, and storage at the OS level providing a platform capable of running infrastructure clouds. The cloud infrastructure is isolated and abstracted away from the underlying physical hardware, enabling multiple cloud environments to be continuously deployed. Cypherpath can be run on private or managed public bare metal for seamless and consistent cloud operations. Create, deploy and run clouds on or off premise anytime, anywhere.
All formats of virtual machine such as KVM, VMDKs, VDIs, qcow2s are supported by our platform. Prebuilt into the solution are Ixia’s full suite of virtualised products that provide the testing, visibility, and security solutions to strengthen your cyber range.
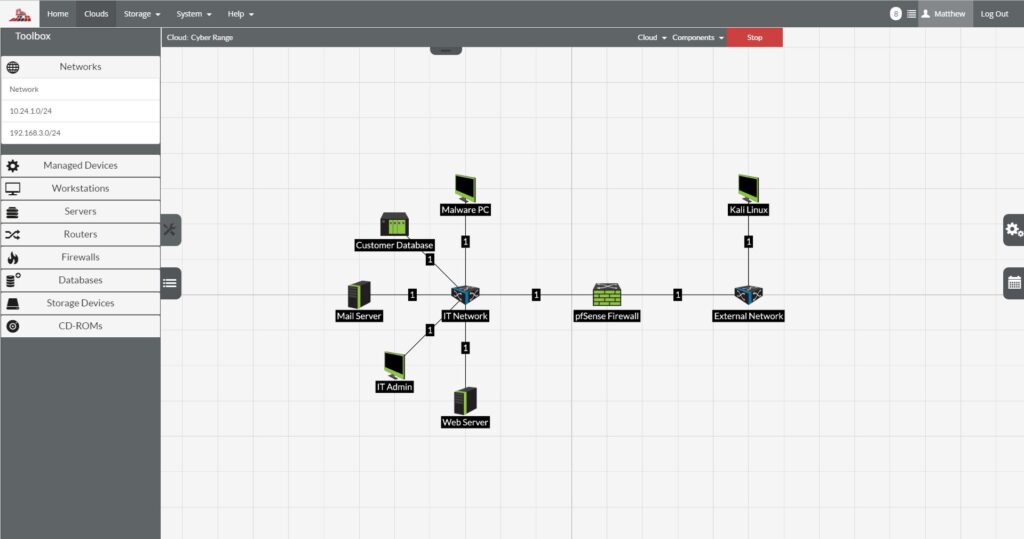
Our on-demand Cyber Range Sandboxes completely models your complex, real-world threat scenarios to ensure you gain the real time visibility into the cause and effect cyber-attacks have on your entity so you can better defend your critical assets.
Key Features
Real Representation of Infrastructure
Use manufacturers like Cisco and Ixia’s virtual machines to create real infrastructure for use in cyber-threat scenarios.
On-Demand
Fully virtualised, the Virtual Test Lab is available on-demand, reusable, easily replicated, and self-service.
Clouds as Files
Each cloud is executed as its own single file and is treated just like a document so it can be edited, copied, shared, and backed up.
Scalability
Scale clouds as needed, on site or in the cloud, and without constraints.
More Agility
Rapidly model even the most complex application and infrastructure configurations; deploy environments on-demand and scale automatically.
Lower Cost
Create virtual infrastructure environments on commodity x86 hardware and use only when needed to maximise capital and operating cost efficiencies.